Slasher Ghost, and Other Developments in Proof of Stake

Particular due to Vlad Zamfir and Zack Hess for ongoing analysis and discussions on proof-of-stake algorithms and their very own enter into Slasher-like proposals
One of the hardest problems in cryptocurrency improvement is that of devising efficient consensus algorithms. Actually, comparatively satisfactory default choices exist. On the very least it’s attainable to depend on a Bitcoin-like proof of work algorithm based mostly on both a randomly-generated circuit approach focused for specialized-hardware resitance, or failing that straightforward SHA3, and our present GHOST optimizations permit for such an algorithm to offer block occasions of 12 seconds. Nevertheless, proof of work as a basic class has many flaws that decision into query its sustainability as an unique supply of consensus; 51% assaults from altcoin miners, eventual ASIC dominance and excessive vitality inefficiency are maybe probably the most distinguished. Over the previous few months we’ve got turn out to be extra and extra satisfied that some inclusion of proof of stake is a needed element for long-term sustainability; nevertheless, really implementing a proof of stake algorithm that’s efficient is proving to be surprisingly complicated.
The truth that Ethereum features a Turing-complete contracting system complicates issues additional, because it makes sure sorts of collusion a lot simpler with out requiring belief, and creates a big pool of stake in the arms of decentralized entities which have the motivation to vote with the stake to gather rewards, however that are too silly to inform good blockchains from dangerous. What the remainder of this text will present is a set of methods that take care of most of the problems surrounding proof of stake algorithms as they exist right this moment, and a sketch of lengthen our present most well-liked proof-of-stake algorithm, Slasher, into one thing rather more sturdy.
Historic Overview: Proof of stake and Slasher
If you happen to’re not but well-versed in the nuances of proof of stake algorithms, first learn:
The basic downside that consensus protocols attempt to clear up is that of making a mechanism for rising a blockchain over time in a decentralized manner that can’t simply be subverted by attackers. If a blockchain doesn’t use a consensus protocol to control block creation, and merely permits anybody so as to add a block at any time, then an attacker or botnet with very many IP addresses might flood the community with blocks, and notably they will use their energy to carry out double-spend assaults – sending a cost for a product, ready for the cost to be confirmed in the blockchain, and then beginning their very own “fork” of the blockchain, substituting the cost that they made earlier with a cost to a distinct account managed by themselves, and rising it longer than the unique so everybody accepts this new blockchain with out the cost as reality.
The final resolution to this downside entails making a block “hard” to create in some style. Within the case of proof of work, every block requires computational effort to provide, and in the case of proof of stake it requires possession of cash – in most instances, it is a probabilistic course of the place block-making privileges are doled out randomly in proportion to coin holdings, and in extra unique “negative block reward” schemes anybody can create a block by spending a sure amount of funds, and they’re compensated through transaction charges. In any of these approaches, every chain has a “score” that roughly displays the entire issue of producing the chain, and the highest-scoring chain is taken to characterize the “truth” at that exact time.
For an in depth overview of some of the finer factors of proof of stake, see the above-linked article; for these readers who’re already conscious of the problems I’ll begin off by presenting a semi-formal specification for Slasher:
- Blocks are produced by miners; in order for a block to be legitimate it should fulfill a proof-of-work situation. Nevertheless, this situation is comparatively weak (eg. we will goal the mining reward to one thing like 0.02x the genesis provide yearly)
- Each block has a set of designated signers, that are chosen beforehand (see beneath). For a block with legitimate PoW to be accepted as half of the chain it should be accompanied by signatures from no less than two thirds of its designated signers.
- When block N is produced, we are saying that the set of potential signers of block N + 3000 is the set of addresses such that sha3(handle + block[N].hash) < block[N].steadiness(handle) * D2 the place D2 is a problem parameter concentrating on 15 signers per block (ie. if block N has lower than 15 signers it goes down in any other case it goes up). Word that the set of potential signers could be very computationally intensive to completely enumerate, and we do not strive to take action; as an alternative we depend on signers to self-declare.
- If a possible signer for block N + 3000 needs to turn out to be a delegated signer for that block, they have to ship a particular transaction accepting this accountability and that transaction should get included between blocks N + 1 and N + 64. The set of designated signers for block N + 3000 is the set of all people that do that. This “signer must confirm” mechanism helps guarantee that almost all of signers will really be on-line when the time involves signal. For blocks 0 … 2999, the set of signers is empty, so proof of work alone suffices to create these blocks.
- When a delegated signer provides their signature to dam N + 3000, they’re scheduled to obtain a reward in block N + 6000.
- If a signer indicators two totally different blocks at peak N + 3000, then if somebody detects the double-signing earlier than block N + 6000 they will submit an “evidence” transaction containing the 2 signatures, destroying the signer’s reward and transferring a 3rd of it to the whistleblower.
- If there may be an inadequate quantity of signers to signal at a specific block peak h, a miner can produce a block with peak h+1 immediately on prime of the block with peak h-1 by mining at an 8x larger issue (to incentivize this, however nonetheless make it much less engaging than attempting to create a traditional block, there’s a 6x larger reward). Skipping over two blocks has larger components of 16x diff and 12x reward, three blocks 32x and 24x, and many others.
Primarily, by explicitly punishing double-signing, Slasher in loads of methods, though not all, makes proof of stake act like a kind of simulated proof of work. An essential incidental profit of Slasher is the non-revert property. In proof of work, typically after one node mines one block another node will instantly mine two blocks, and so some nodes might want to revert again one block upon seeing the longer chain. Right here, each block requires two thirds of the signers to ratify it, and a signer can not ratify two blocks on the identical peak with out shedding their features in each chains, so assuming no malfeasance the blockchain won’t ever revert. From the purpose of view of a decentralized utility developer, this can be a very fascinating property because it implies that “time” solely strikes in one course, similar to in a server-based setting.
Nevertheless, Slasher continues to be weak to 1 explicit class of assault: long-range assaults. As an alternative of attempting to begin a fork from ten blocks behind the present head, suppose that an attacker tries to begin a fork ranging from ten thousand blocks behind, and even the genesis block – all that issues is that the depth of the fork should be larger than the period of the reward lockup. At that time, as a result of customers’ funds are unlocked and they will transfer them to a brand new handle to flee punishment, customers haven’t any disincentive towards signing on each chains. The truth is, we could even anticipate to see a black market of individuals promoting their outdated personal keys, culminating with an attacker single-handedly buying entry to the keys that managed over 50% of the forex provide sooner or later in historical past.
One strategy to fixing the long-range double-signing downside is transactions-as-proof-of-stake, another PoS resolution that doesn’t have an incentive to double-sign as a result of it is the transactions that vote, and there isn’t any reward for sending a transaction (in truth there is a price, and the reward is exterior the community); nevertheless, this does nothing to cease the black key market downside. To correctly take care of that difficulty, we might want to chill out a hidden assumption.
Subjective Scoring and Belief
For all its faults, proof of work does have some elegant financial properties. Significantly, as a result of proof of work requires an externally rivalrous useful resource, one thing with exists and is consumed exterior the blockchain, in order to generate blocks (specifically, computational effort), launching a fork towards a proof of work chain invariably requires accessing, and spending, a big amount of financial sources. Within the case of proof of stake, alternatively, the one scarce worth concerned is worth throughout the chain, and between a number of chains that worth will not be scarce in any respect. It doesn’t matter what algorithm is used, in proof of stake 51% of the house owners of the genesis block might ultimately come collectively, collude, and produce an extended (ie. higher-scoring) chain than everybody else.
This may increasingly look like a deadly flaw, however in actuality it is just a flaw if we implicitly settle for an assumption that’s made in the case of proof of work: that nodes haven’t any information of historical past. In a proof-of-work protocol, a brand new node, having no direct information of previous occasions and seeing nothing however the protocol supply code and the set of messages which have already been printed, can be a part of the community at any level and decide the rating of all attainable chains, and from there the block that’s on the prime of the highest-scoring predominant chain. With proof of stake, as we described, such a property can’t be achieved, since it’s extremely low-cost to accumulate historic keys and simulate alternate histories. Thus, we are going to chill out our assumptions considerably: we are going to say that we’re solely involved with sustaining consensus between a static set of nodes which might be on-line no less than as soon as each N days, permitting these nodes to make use of their very own information of historical past to reject apparent long-range forks utilizing some method, and new nodes or long-dormant nodes might want to specify a “checkpoint” (a hash of a block representing what the remainder of the community agrees is a latest state) in order to get again onto the consensus.
Such an strategy is actually a hybrid between the pure and maybe harsh trust-no-one logic of Bitcoin and the entire dependency on socially-driven consensus discovered in networks like Ripple. In Ripple’s case, customers becoming a member of the system want to pick out a set of nodes that they belief (or, extra exactly, belief to not collude) and depend on these nodes throughout each step of the consensus course of. Within the case of Bitcoin, the idea is that no such belief is required and the protocol is totally self-contained; the system works simply as properly between a thousand remoted cavemen with laptops on a thousand islands because it does in a strongly related society (in truth, it’d work higher with island cavemen, since with out belief collusion is harder). In our hybrid scheme, customers want solely look to the society exterior of the protocol precisely as soon as – once they first obtain a shopper and discover a checkpoint – and can take pleasure in Bitcoin-like belief properties ranging from that time.
In an effort to decide which belief assumption is the higher one to take, we in the end have to ask a considerably philosophical query: do we would like our consensus protocols to exist as absolute cryptoeconomic constructs utterly impartial of the skin world, or are we okay with relying closely on the truth that these programs exist in the context of a wider society? Though it’s certainly a central tenet of mainstream cryptocurrency philosophy that an excessive amount of exterior dependence is harmful, arguably the extent of independence that Bitcoin affords us in actuality is not any larger than that supplied by the hybrid mannequin. The argument is straightforward: even in the case of Bitcoin, a consumer should additionally take a leap of belief upon becoming a member of the community – first by trusting that they’re becoming a member of a protocol that accommodates property that different individuals discover invaluable (eg. how does a consumer know that bitcoins are price $380 every and dogecoins solely $0.0004? Particularly with the totally different capabilities of ASICs for various algorithms, hashpower is simply a really tough estimate), and second by trusting that they’re downloading the right software program bundle. In each the supposedly “pure” mannequin and the hybrid mannequin there may be at all times a have to look exterior the protocol precisely as soon as. Thus, on the entire, the achieve from accepting the additional belief requirement (specifically, environmental friendliness and safety towards oligopolistic mining swimming pools and ASIC farms) is arguably price the associated fee.
Moreover, we could observe that, in contrast to Ripple consensus, the hybrid mannequin continues to be appropriate with the concept of blockchains “talking” to every one another by containing a minimal “light” implementation of one another’s protocols. The reason being that, whereas the scoring mechanism will not be “absolute” from the purpose of view of a node with out historical past immediately taking a look at each block, it’s completely enough from the purpose of view of an entity that is still on-line over a protracted interval of time, and a blockchain actually is such an entity.
To date, there have been two main approaches that adopted some type of checkpoint-based belief mannequin:
- Developer-issued checkpoints – the shopper developer points a brand new checkpoint with every shopper improve (eg. used in PPCoin)
- Revert restrict – nodes refuse to simply accept forks that revert greater than N (eg. 3000) blocks (eg. used in Tendermint)
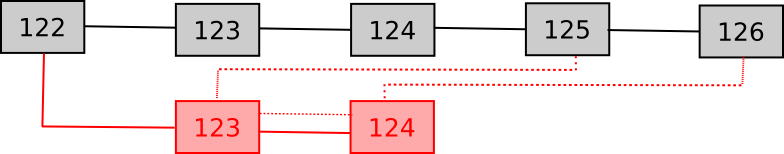
The primary strategy has been roundly criticized by the cryptocurrency group for being too centralized. The second, nevertheless, additionally has a flaw: a robust attacker cannot solely revert just a few thousand blocks, but additionally probably cut up the community completely. Within the N-block revert case, the technique is as follows. Suppose that the community is at the moment at block 10000, and N = 3000. The attacker begins a secret fork, and grows it by 3001 blocks sooner than the primary community. When the primary community will get to 12999, and some node produces block 13000, the attacker reveals his personal fork. Some nodes will see the primary community’s block 13000, and refuse to change to the attacker’s fork, however the nodes that didn’t but see that block will probably be glad to revert from 12999 to 10000 and then settle for the attacker’s fork. From there, the community is completely cut up.
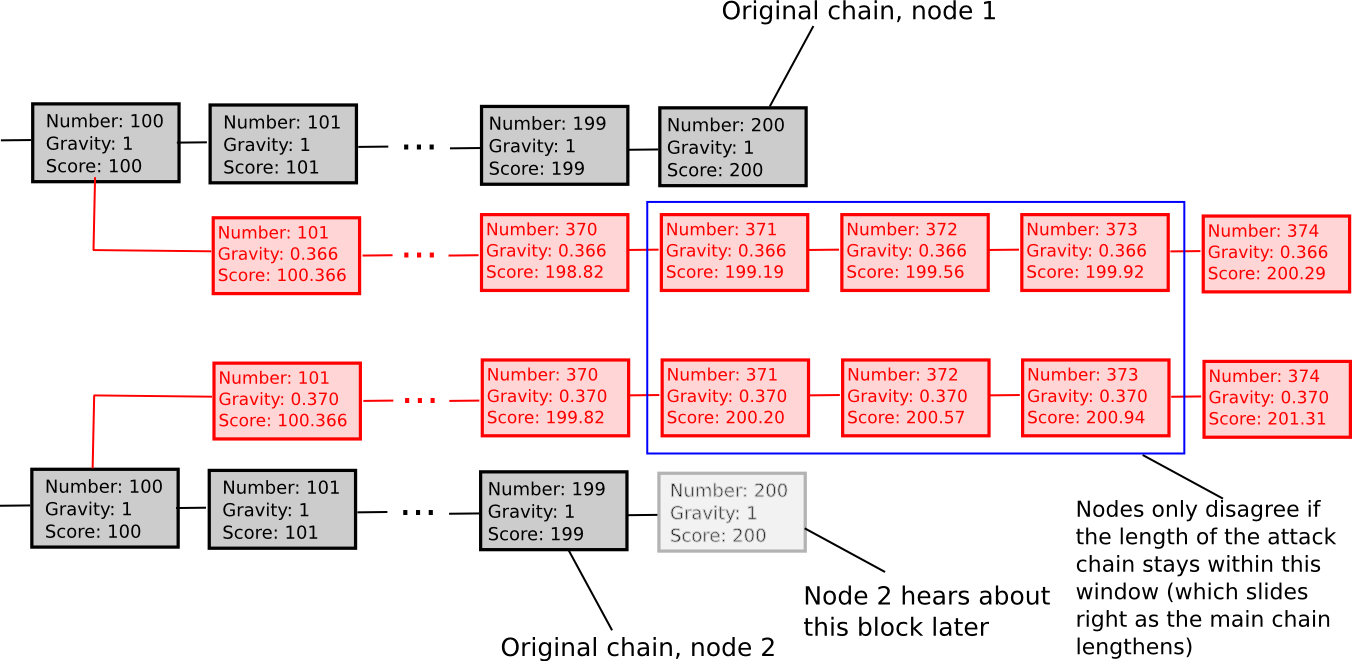
Thankfully, one can really assemble a 3rd strategy that neatly solves this downside, which we are going to name exponentially subjective scoring. Primarily, as an alternative of rejecting forks that return too far, we merely penalize them on a graduating scale. For each block, a node maintains a rating and a “gravity” issue, which acts as a multiplier to the contribution that the block makes to the blockchain’s rating. The gravity of the genesis block is 1, and usually the gravity of another block is about to be equal to the gravity of its father or mother. Nevertheless, if a node receives a block whose father or mother already has a sequence of N descendants (ie. it is a fork reverting N blocks), that block’s gravity is penalized by an element of 0.99N, and the penalty propagates endlessly down the chain and stacks multiplicatively with different penalties.
That’s, a fork which begins 1 block in the past might want to develop 1% sooner than the primary chain in order to overhaul it, a fork which begins 100 blocks in the past might want to develop 2.718 occasions as shortly, and a fork which begins 3000 blocks in the past might want to develop 12428428189813 occasions as shortly – clearly an impossibility with even trivial proof of work.
The algorithm serves to easy out the function of checkpointing, assigning a small “weak checkpoint” function to every particular person block. If an attacker produces a fork that some nodes hear about even three blocks sooner than others, these two chains might want to keep inside 3% of one another endlessly in order for a community cut up to take care of itself.
There are different options that might be used apart from, and even alongside ESS; a specific set of methods entails stakeholders voting on a checkpoint each few thousand blocks, requiring each checkpoint produced to replicate a big consensus of the bulk of the present stake (the explanation the bulk of the stake cannot vote on each block is, of course, that having that many signatures would bloat the blockchain).
Slasher Ghost
The opposite giant complexity in implementing proof of stake for Ethereum particularly is the truth that the community features a Turing-complete monetary system the place accounts can have arbitrary permissions and even permissions that change over time. In a easy forex, proof of stake is comparatively simple to perform as a result of every unit of forex has an unambiguous proprietor exterior the system, and that proprietor might be counted on to take part in the stake-voting course of by signing a message with the personal key that owns the cash. In Ethereum, nevertheless, issues should not fairly so easy: if we do our job selling correct pockets safety proper, the bulk of ether goes to be saved in specialised storage contracts, and with Turing-complete code there isn’t any clear manner of ascertaining or assigning an “owner”.
One technique that we checked out was delegation: requiring each handle or contract to assign an handle as a delegate to signal for them, and that delegate account must be managed by a personal key. Nevertheless, there’s a downside with any such strategy. Suppose {that a} majority of the ether in the system is definitely saved in utility contracts (versus private storage contracts); this contains deposits in SchellingCoins and different stake-based protocols, safety deposits in probabilistic enforcement programs, collateral for monetary derivatives, funds owned by DAOs, and many others. These contracts would not have an proprietor even in spirit; in that case, the concern is that the contract will default to a technique of renting out stake-voting delegations to the very best bidder. As a result of attackers are the one entities keen to bid greater than the anticipated return from the delegation, it will make it very low-cost for an attacker to accumulate the signing rights to giant portions of stake.
The one resolution to this throughout the delegation paradigm is to make it extraordinarily dangerous to dole out signing privileges to untrusted events; the best strategy is to switch Slasher to require a big deposit, and slash the deposit in addition to the reward in the occasion of double-signing. Nevertheless, if we do that then we’re primarily again to entrusting the destiny of a big amount of funds to a single personal key, thereby defeating a lot of the purpose of Ethereum in the primary place.
Thankfully, there may be one different to delegation that’s considerably more practical: letting contracts themselves signal. To see how this works, take into account the next protocol:
- There’s now a SIGN opcode added.
- A signature is a sequence of digital transactions which, when sequentially utilized to the state on the finish of the father or mother block, outcomes in the SIGN opcode being known as. The nonce of the primary VTX in the signature should be the prevhash being signed, the nonce of the second should be the prevhash plus one, and so forth (alternatively, we will make the nonces -1, -2, -3 and many others. and require the prevhash to be handed in by transaction information in order to be ultimately provided as an enter to the SIGN opcode).
- When the block is processed, the state transitions from the VTXs are reverted (that is what is supposed by “virtual”) however a deposit is subtracted from every signing contract and the contract is registered to obtain the deposit and reward in 3000 blocks.
Principally, it’s the contract’s job to find out the entry coverage for signing, and the contract does this by inserting the SIGN opcode behind the suitable set of conditional clauses. A signature now turns into a set of transactions which collectively fulfill this entry coverage. The inducement for contract builders to maintain this coverage safe, and not dole it out to anybody who asks, is that if it’s not safe then somebody can double-sign with it and destroy the signing deposit, taking a portion for themselves as per the Slasher protocol. Some contracts will nonetheless delegate, however that is unavoidable; even in proof-of-stake programs for plain currencies comparable to NXT, many customers find yourself delegating (eg. DPOS even goes as far as to institutionalize delegation), and no less than right here contracts have an incentive to delegate to an entry coverage that’s not more likely to come below the affect of a hostile entity – in truth, we could even see an equilibrium the place contracts compete to ship safe blockchain-based stake swimming pools which might be least more likely to double-vote, thereby rising safety over time.
Nevertheless, the virtual-transactions-as-signatures paradigm does impose one complication: it’s not trivial to offer an proof transaction displaying two signatures by the identical signer on the identical block peak. As a result of the outcome of a transaction execution depends upon the beginning state, in order to determine whether or not a given proof transaction is legitimate one should show the whole lot as much as the block in which the second signature was given. Thus, one should primarily “include” the fork of a blockchain inside of the primary chain. To do that effectively, a comparatively easy proposal is a kind of “Slasher GHOST” protocol, the place one can embody side-blocks in the primary chain as uncles. Particularly, we declare two new transaction sorts:
- [block_number, uncle_hash] – this transaction is legitimate if (1) the block with the given uncle_hash has already been validated, (2) the block with the given uncle_hash has the given block quantity, and (3) the father or mother of that uncle is both in the primary chain or was included earlier as an uncle. In the course of the act of processing this transaction, if addresses that double-signed at that peak are detected, they’re appropriately penalized.
- [block_number, uncle_parent_hash, vtx] – this transaction is legitimate if (1) the block with the given uncle_parent_hash has already been validated, (2) the given digital transaction is legitimate on the given block peak with the state on the finish of uncle_parent_hash, and (3) the digital transaction reveals a signature by an handle which additionally signed a block on the given block_number in the primary chain. This transaction penalizes that one handle.
Primarily, one can assume of the mechanism as working like a “zipper”, with one block from the fork chain at a time being zipped into the primary chain. Word that for a fork to begin, there should exist double-signers at each block; there isn’t any scenario the place there’s a double-signer 1500 blocks right into a fork so a whistleblower should “zip” 1499 harmless blocks into a sequence earlier than attending to the goal block – moderately, in such a case, even when 1500 blocks must be added, every one of them notifies the primary chain about 5 separate malfeasors that double-signed at that peak. One considerably sophisticated property of the scheme is that the validity of these “Slasher uncles” depends upon whether or not or not the node has validated a specific block exterior of the primary chain; to facilitate this, we specify {that a} response to a “getblock” message in the wire protocol should embody the uncle-dependencies for a block earlier than the precise block. Word that this may occasionally typically result in a recursive growth; nevertheless, the denial-of-service potential is proscribed since every particular person block nonetheless requires a considerable amount of proof-of-work to provide.
Blockmakers and Overrides
Lastly, there’s a third complication. Within the hybrid-proof-of-stake model of Slasher, if a miner has an awesome share of the hashpower, then the miner can produce a number of variations of every block, and ship totally different variations to totally different components of the community. Half the signers will see and signal one block, half will see and signal one other block, and the community will probably be caught with two blocks with inadequate signatures, and no signer keen to slash themselves to finish the method; thus, a proof-of-work override will probably be required, a harmful scenario for the reason that miner controls most of the proof-of-work. There are two attainable options right here:
- Signers ought to wait just a few seconds after receiving a block earlier than signing, and solely signal stochastically in some style that ensures {that a} random one of the blocks will dominate.
- There needs to be a single “blockmaker” among the many signers whose signature is required for a block to be legitimate. Successfully, this transfers the “leadership” function from a miner to a stakeholder, eliminating the issue, however on the price of including a dependency on a single social gathering that now has the power to considerably inconvenience everybody by not signing, or unintentionally by being the goal of a denial-of-service assault. Such conduct might be disincentivized by having the signer lose half of their deposit if they don’t signal, however even nonetheless it will outcome in a moderately jumpy block time if the one approach to get round an absent blockmaker is utilizing a proof-of-work override.
One attainable resolution to the issue in (2) is to take away proof of work solely (or nearly solely, retaining a minimal quantity for anti-DDoS worth), changing it with a mechanism that Vlad Zamfir has coined “delegated timestamping”. Primarily, each block should seem on schedule (eg. at 15 second intervals), and when a block seems the signers vote 1 if the block was on time, or 0 if the block was too early or too late. If the bulk of the signers votes 0, then the block is handled as invalid – stored in the chain in order to present the signers their truthful reward, however the blockmaker will get no reward and the state transition will get omitted. Voting is incentivized through schellingcoin – the signers whose vote agrees with the bulk get an additional reward, so assuming that everybody else goes to be sincere everybody has the motivation to be sincere, in a self-reinforcing equilibrium. The speculation is {that a} 15-second block time is just too quick for signers to coordinate on a false vote (the astute reader could observe that the signers have been determined 3000 blocks in advance so this isn’t actually true; to repair this we will create two teams of signers, one pre-chosen group for validation and one other group chosen at block creation time for timestamp voting).
Placing all of it Collectively
Taken collectively, we will thus see one thing like the next working as a practical model of Slasher:
- Each block has a designated blockmaker, a set of designated signers, and a set of designated timestampers. For a block to be accepted as half of the chain it should be accompanied by virtual-transactions-as-signatures from the blockmaker, two thirds of the signers and 10 timestampers, and the block will need to have some minimal proof of work for anti-DDoS causes (say, focused to 0.01x per 12 months)
- Throughout block N, we are saying that the set of potential signers of block N + 3000 is the set of addresses such that sha3(handle + block[N].hash) < block[N].steadiness(handle) * D2 the place D2 is a problem parameter concentrating on 15 signers per block (ie. if block N has lower than 15 signers it goes down in any other case it goes up).
- If a possible signer for block N + 3000 needs to turn out to be a signer, they have to ship a particular transaction accepting this accountability and supplying a deposit, and that transaction should get included between blocks N + 1 and N + 64. The set of designated signers for block N + 3000 is the set of all people that do that, and the blockmaker is the designated signer with the bottom worth for sha3(handle + block[N].hash). If the signer set is empty, no block at that peak might be made. For blocks 0 … 2999, the blockmaker and solely signer is the protocol developer.
- The set of timestampers of the block N + 3000 is the set of addresses such that sha3(handle + block[N].hash) < block[N].steadiness(handle) * D3, the place D3 is focused such that there’s a mean of 20 timestampers every block (ie. if block N has lower than 20 timestampers it goes down in any other case it goes up).
- Let T be the timestamp of the genesis block. When block N + 3000 is launched, timestampers can provide virtual-transactions-as-signatures for that block, and have the selection of voting 0 or 1 on the block. Voting 1 implies that they noticed the block inside 7.5 seconds of time T + (N + 3000) * 15, and voting 0 implies that they acquired the block when the time was exterior that vary. Word that nodes ought to detect if their clocks are out of sync with everybody else’s clocks on the blockchain, and if that’s the case modify their system clocks.
- Timestampers who voted together with the bulk obtain a reward, different timestampers get nothing.
- The designated signers for block N + 3000 have the power to signal that block by supplying a set of virtual-transactions-as-a-signature. All designated signers who signal are scheduled to obtain a reward and their returned deposit in block N + 6000. Signers who skipped out are scheduled to obtain their returned deposit minus twice the reward (which means it is solely economically worthwhile to enroll as a signer in the event you really assume there’s a probability larger than 2/3 that you can be on-line).
- If the bulk timestamper vote is 1, the blockmaker is scheduled to obtain a reward and their returned deposit in block N + 6000. If the bulk timestamper vote is 0, the blockmaker is scheduled to obtain their deposit minus twice the reward, and the block is ignored (ie. the block is in the chain, however it doesn’t contribute to the chain’s rating, and the state of the following block begins from the top state of the block earlier than the rejected block).
- If a signer indicators two totally different blocks at peak N + 3000, then if somebody detects the double-signing earlier than block N + 6000 they will submit an “evidence” transaction containing the 2 signatures to both or each chains, destroying the signer’s reward and deposit and transferring a 3rd of it to the whistleblower.
- If there may be an inadequate quantity of signers to signal or the blockmaker is lacking at a specific block peak h, the designated blockmaker for peak h + 1 can produce a block immediately on prime of the block at peak h – 1 after ready for 30 seconds as an alternative of 15.
After years of analysis, one factor has turn out to be clear: proof of stake is non-trivial – so non-trivial that some even consider it impossible. The problems of nothing-at-stake and long-range assaults, and the shortage of mining as a rate-limiting system, require a quantity of compensatory mechanisms, and even the protocol above doesn’t handle the problem of randomly choose signers. With a considerable proof of work reward, the issue is proscribed, as block hashes is usually a supply of randomness and we will mathematically present that the achieve from holding again block hashes till a miner finds a hash that favorably selects future signers is normally lower than the achieve from publishing the block hashes. With out such a reward, nevertheless, different sources of randomness comparable to low-influence features must be used.
For Ethereum 1.0, we take into account it extremely fascinating to each not excessively delay the discharge and not strive too many untested options without delay; therefore, we are going to seemingly follow ASIC-resistant proof of work, maybe with non-Slasher proof of activity as an addon, and have a look at transferring to a extra complete proof of stake mannequin over time.